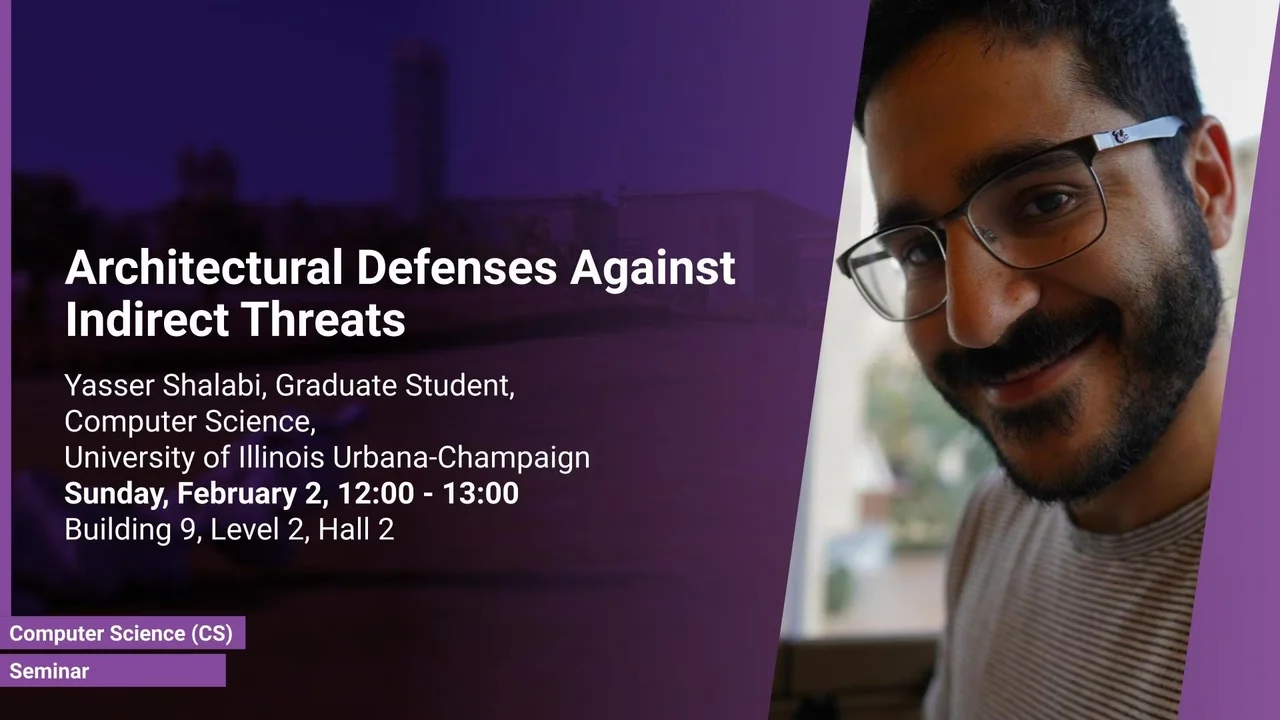
Architectural Defenses against Indirect Threats
- Yasser Shalabi, Graduate Student, Computer Science, University of Illinois Urbana-Champaign
B9 L2 H2
The potential of indirect execution attacks – e.g. Return-Oriented-Programming and Transient-Execution based Side-channels – threaten all modern computing platforms. Standard security policies are unable to eliminate these threats. What is the role of hardware in mitigating these threats? Why are the latest processor designs no longer proactively eliminating threats? In this talk, we will explore these questions and reconsider the role of hardware in securing systems. I will present Record-and-Replay as a fundamental solution that can enable a hardware-software co-design that can strengthen the security of modern computing platforms.
Overview
Abstract
The potential of indirect execution attacks – e.g. Return-Oriented-Programming and Transient-Execution based Side-channels – threaten all modern computing platforms. Standard security policies are unable to eliminate these threats. What is the role of hardware in mitigating these threats? Why are the latest processor designs no longer proactively eliminating threats? In this talk, we will explore these questions and reconsider the role of hardware in securing systems. I will present Record-and-Replay as a fundamental solution that can enable a hardware-software co-design that can strengthen the security of modern computing platforms.
Brief Biography
Yasser graduates from UIUC in 2020 after having defended his Ph.D. thesis in December 2019. Prior to graduate school he worked at Intel as a software developer. He does research within the intersections of program security, systems, and computer architecture. He has developed techniques that mitigate threats related to return-oriented programming and architectural side-channel attacks. Lately, he has been working on leveraging hardware-accelerated tracing to enable anomaly detection based security systems.