Tackling credential abuse together
Despite long-ago predictions (e.g., see Bill Gates, 2004) that other user-authentication technologies would replace passwords, passwords remain not only pervasive but have flourished as the dominant form of account protection, especially at websites such as retailers that require a low-friction user experience. This talk will describe our research on methods to tackle three key ingredients of account takeovers for password-protected accounts today: (i) site database breaches, which is the largest source of stolen passwords for internet sites; (ii) the tendency of users to reuse the same or similar passwords across sites; and (iii) credential stuffing, in which attackers submit breached credentials for one site in login attempts for the same users' accounts at another.
Overview
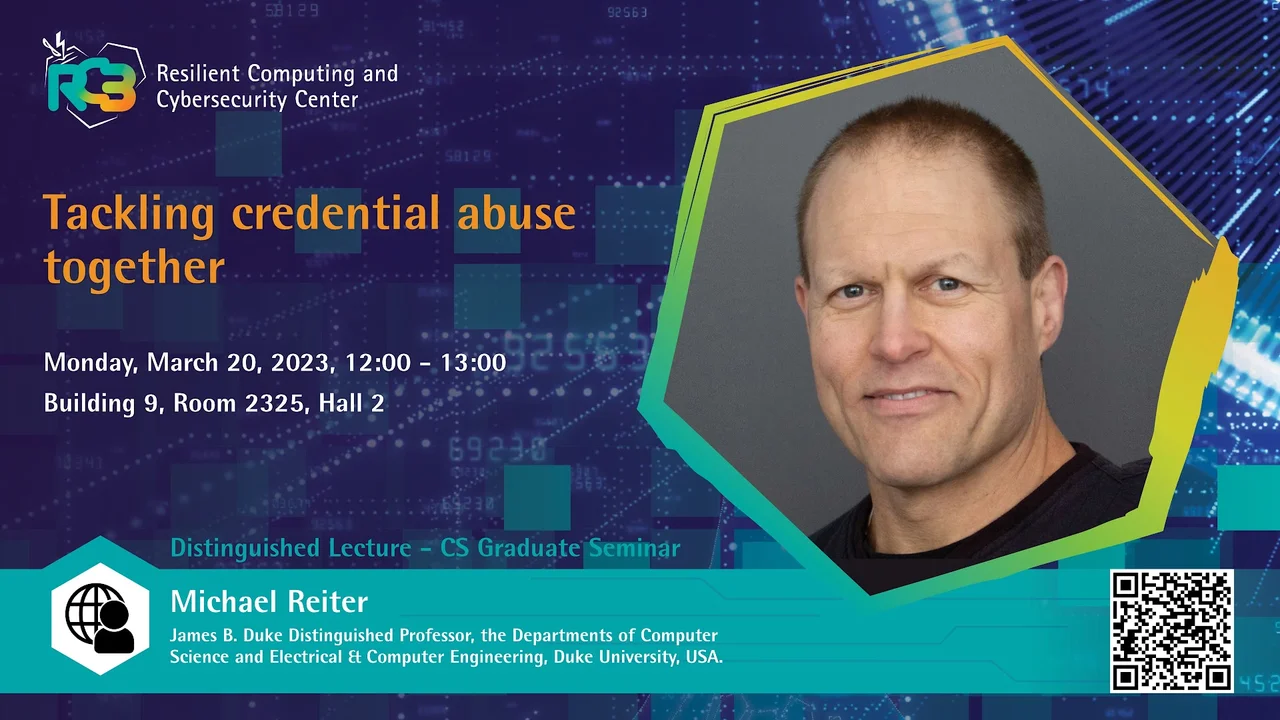
This Distinguished Lecture is part of the CS Graduate Seminars.
Abstract
Despite long-ago predictions (e.g., see Bill Gates, 2004) that other user-authentication technologies would replace passwords, passwords remain not only pervasive but have flourished as the dominant form of account protection, especially at websites such as retailers that require a low-friction user experience. This talk will describe our research on methods to tackle three key ingredients of account takeovers for password-protected accounts today: (i) site database breaches, which is the largest source of stolen passwords for internet sites; (ii) the tendency of users to reuse the same or similar passwords across sites; and (iii) credential stuffing, in which attackers submit breached credentials for one site in login attempts for the same users' accounts at another. A central theme of our research is that these factors are most effectively addressed by coordinating across sites, in contrast to today's practice of each site defending alone. We describe algorithms to drive this coordination, demonstrate the efficacy and security of our proposals through conservative analyses, and demonstrate the scalability of our designs through working implementations. This research was performed jointly with Ke Coby Wang.
Brief Biography
Michael Reiter is a James B. Duke Distinguished Professor in the Departments of Computer Science and Electrical & Computer Engineering at Duke University, which he joined in January 2021 following previous positions in industry (culminating as Director of Secure Systems Research at Bell Labs, Lucent) and academia (Professor of CS and ECE at Carnegie Mellon, and Distinguished Professor of CS at UNC-Chapel Hill). His technical contributions lie primarily in computer security and distributed computing and include several that have seen widespread adoption. He is a Fellow of the ACM and IEEE, winner of the ACM SIGSAC Outstanding Contributions Award, and two-time winner of the Test-of-Time Award from the ACM Conference on Computer and Communications Security, for research papers that have had long-lasting influence.