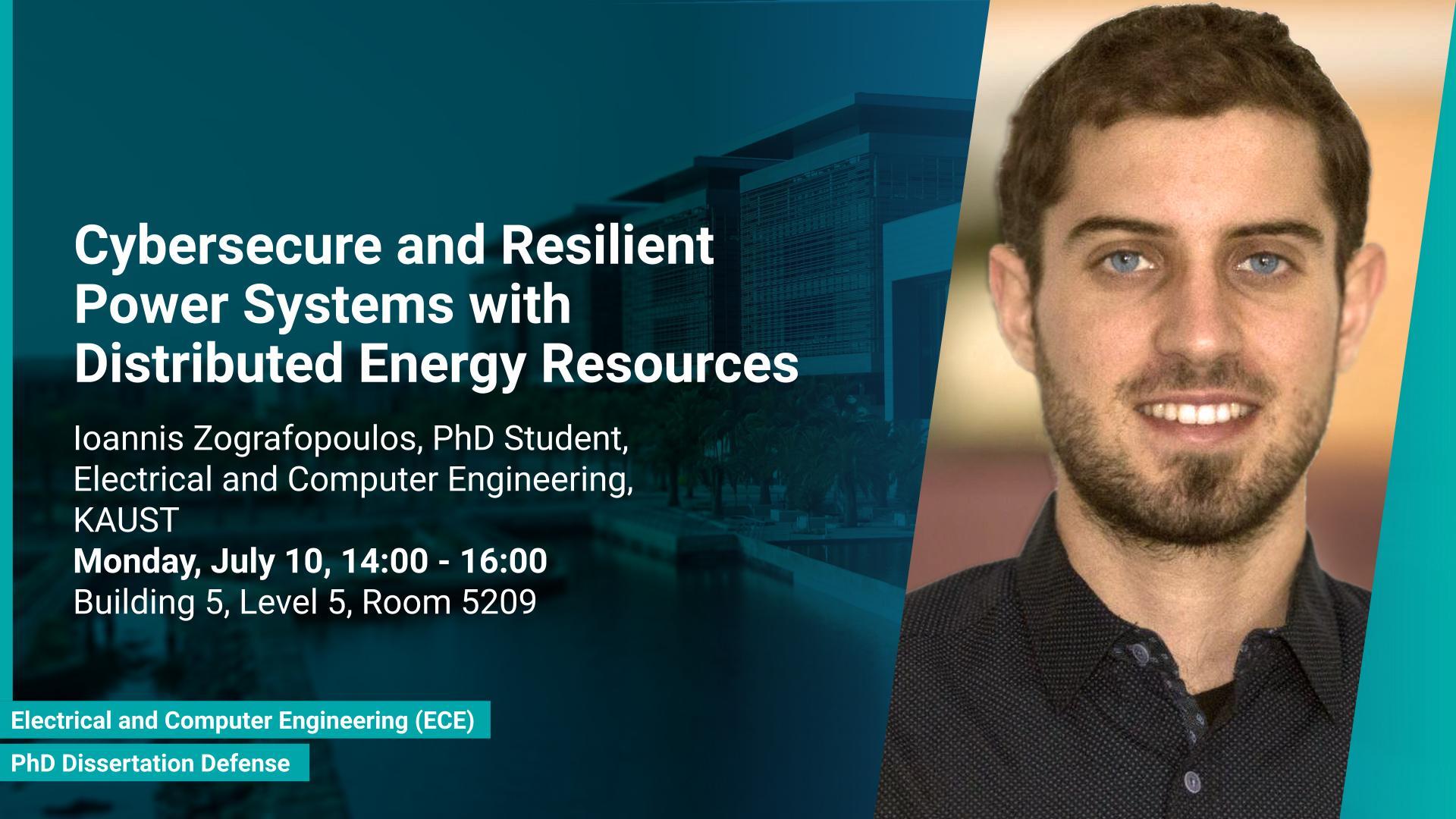
Monday, July 10, 2023, 14:00
- 16:00
Building 5, Level 5, Room 5209
Contact Person
Power systems constitute a pillar of the critical infrastructure, and, as a result, their cybersecurity is paramount. Traditional power system architectures are moving from their original centralized nature to a distributed paradigm. This transition has been propelled by the rapid penetration of distributed energy resources (DERs) such as rooftop solar panels, battery storage, etc. However, with the introduction of new DER devices, the threat surface of power systems is inadvertently expanding.

![ECCS Workshop-Galymzhan Nauryzbayev- 28 Nov 2022 [22].pptx-3.jpg](/sites/default/files/styles/max_fullhd_scale/public/2022-11/ECCS%20Workshop-Galymzhan%20Nauryzbayev-%2028%20Nov%202022%20%5B22%5D.pptx-3.jpg?itok=sPZpIFoE)


![ECCS Workshop-Mohammad AlFaruque- 27 Nov 2022 [22].pptx_.jpg](/sites/default/files/styles/max_fullhd_scale/public/2022-11/ECCS%20Workshop-Mohammad%20AlFaruque-%2027%20Nov%202022%20%5B22%5D.pptx_.jpg?itok=2YLWv_mQ)